06/10/20: Post created based on AirWatch console version 9.1.1. However, the steps are the same in the latest console version including 20.07.
Apple may hate me for this, VMware AirWatch doesn’t support this, and some of us in the mobile community may not agree with this practice either. I think due to mounting pressure, Apple has finally given admins the ability to block iOS update for a minimum of 30 days or up to 90 days starting with iOS 11.3.
However, sometimes installing the latest iOS update can cause more headache than good such as the two issues below:
- iOS 11.3 devices causing VPP applications to be removed
- Critical issue advisory – Cannot activate iOS 11.3 devices on BlackBerry UEM
By default, iOS update will be downloaded in the background if the device is connected to WiFi. To block the iOS update from being downloaded altogether, we will modify the Global HTTP Proxy for the network connection on the device.
To take advantage of this feature, here are the prerequisites:
- Your device must be supervised.
- You need a web server that is accessible by iOS devices to host a PAC file or use the link provided via this post.
The idea of using a PAC file is to re-direct iOS update to a dummy/inaccessible site.
Here is the content of the current PAC file:
function FindProxyForURL(url, host)
{
if (host ==”mesu.apple.com”)
return “PROXY 127.0.0.2:8080”;
if (host ==”appldnld.apple.com”)
return “PROXY 127.0.0.2:8080”;
else return “DIRECT”;
}
Here is further explanation of the existing PAC file used:
- mesu.apple.com – Apple’s Mobile Asset Software Update service. Provides an XML file with information about available iOS updates. When blocked, devices cannot determine that a new update is available.
- appldnld.apple.com – (Optional) Apple’s iOS and software repository. Where devices will actually download the iOS update from. However, other software and updates are also provided by this URL. Blocking may not be desirable in all environments.
- Source: https://documentation.meraki.com/zGeneral_Administration/Other_Topics/Blocking_or_rate_limiting_iOS_updates
Let’s take a look at the steps required.
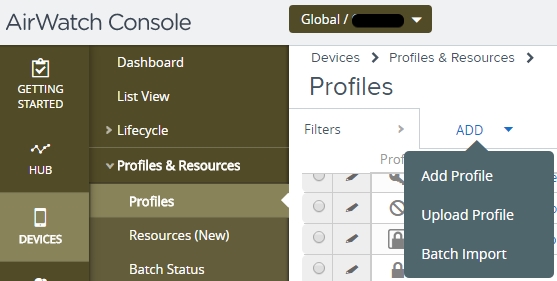
- Log onto AirWatch console. Then go to DEVICES -> Profiles & Resources -> Profiles, click ADD -> Add Profile
- Select the applicable platform. For this example, we select iOS.

- Fill out both the General section accordingly.
- Scroll down to Global HTTP Proxy and click on the Configure button
- In here, configure as follow. Then click Save & Publish
- Gateway Platform – Auto
- Proxy PAC File URL – URL where your PAC file is located. You may also use the one here shared by another fellow admin, Nick G. with Bluewater Technologies: https://s3.amazonaws.com/bwt-deployments/GM/OTA-Block.pac
- If the file above is no longer available, use notepad and include the content below. Then, save it with .pac extension.
function FindProxyForURL(url, host) {
if (host ==”mesu.apple.com”) return “PROXY 127.0.0.2:8080”;
if (host ==”appldnld.apple.com”) return “PROXY 127.0.0.2:8080”;
if (host ==”updates-http.cdn-apple.com”) return “PROXY 127.0.0.2:8080”;
else return “DIRECT”; }
- Leave the other two boxes unchecked

With this setup, users assigned to this profile are blocked from being able to check for newest iOS release.
- If the iOS update is already downloaded prior to this setup, the user can still install accordingly.
- AirWatch admin will not be able to schedule iOS update either from the web console.
On the device itself, the section “HTTP PROXY” is not available as it is now configured by the profile above.
Before the profile is assigned to the device:

After the profile is assigned to the device:

When the user attempts to check for iOS update, it will fail and display the error prompt below.

I am often asked if this blocks app update as well. Here’s my answer:
- No, as the entries to block app (.ipa) is not present in the PAC file
- The entry is phobos.apple.com
- An app can still be pushed/re-pushed from AirWatch console via VPP
Hope you find this post helpful!

[…] AirWatch admins, I’ve shared the steps to stop iOS update on its track. And if you are lucky enough to be running Blackberry UEM 12.8, you are not affected by this issue […]
LikeLike
[…] I shared the steps to stop iOS update in response to numerous issues with each new iOS release. Now, let me share the steps to schedule […]
LikeLike
[…] Stop iOS update on its track with VMware AirWatch […]
LikeLike
[…] Stop iOS update on its track with VMware AirWatch […]
LikeLike
I am trying to block on iPADs , it worked good but code stopped as of 11/16/2022.
I have added all required host servers,
my PAC code
function FindProxyForURL(url, host) {
if (host ==”mesu.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”https://mesu.apple.com”) return “PROXY 127.0.0.1:8081″;
if (host ==”www.mesu.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”gdmf.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”https://gdmf.apple.com”) return “PROXY 127.0.0.1:8081″;
if (host ==”www.gdmf.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”appldnld.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”xp.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”gg.apple.com”) return “PROXY 127.0.0.2:8080″;
if (host ==”gs.apple.com”) return “PROXY 127.0.0.2:8080”;
else return “DIRECT”; }
LikeLike