Updated from 03/26/20: The KB below is highly recommended for the most up-to-date information for this setup.
Deploying VMware Workspace ONE Tunnel: VMware Workspace ONE Operational Tutorial
Post created based on AirWatch console version 9.1.1 and VMware Unified Access Gateway 3.1.1.
As the mobile landscape continues to grow, we have come to enjoy the convenience of accessing just what we need anytime and anywhere right from our smartphones. While mobile devices may not replace the true desktop experience required by many professionals (i.e. graphic artists, computer programmers, etc.), they do more or less give us the freedom to stay connected without being physically connected.
In the past, access to work resources remotely is more or less limited to either traditional VPN or Citrix. The problem with traditional VPN is that once the connection establishes, the entire mobile device (smartphone, laptop or even desktop) becomes part of the network. This may not be ideal especially if any of these endpoints become compromised with a virus, malware, etc. Not to mention information security team may require several security-related add-ins, such as McAfee DLP, installed on the device prior to granting the remote privilege.
On the other hand, launching the application through Citrix may be cumbersome with having to launch the Citrix Receiver first follow by the app itself.
With VMware AirWatch Per-App VPN, users can now access specific work resources through specific apps right from their mobile devices quickly and securely without either traditional VPN or Citrix. With this setup, the user experience will be the same as launching any mobile app to check email, look up weather information, etc. Let me show you how.
While this might be a lengthy setup process, it’s almost maintenance-free except for future version upgrade. As my network admin likes to say: I’m only a plumber and everything else is up to the application owner. This is no different at all.
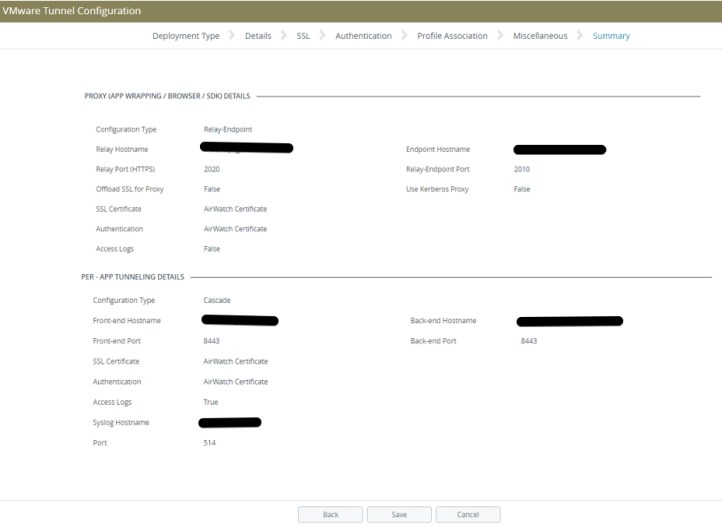
For this setup, we go with the Cascade deployment model which is formerly known as the Relay-Endpoint deployment model. You can learn more about this model here.

To start, navigate to Groups & Settings > All Settings > System > Advanced > API > REST API. Select the Override radio button next to Current Setting. Then click Save.

Next, navigate to System > Enterprise Integration -> VMware Tunnel -> Configuration.
Next to VMware Tunnel, click Enabled. Then click Configure at the bottom of the page.

Within VMware Tunnel Configuration, click Enabled next to Per-App Tunnel (Linux Only) and select Cascade from the drop down menu.

Fill in both front-end and back-end hostname. By default, the port number is 8443.

You can accept the default setting on the remaining screens, or modify accordingly to suit your environment.


Click OK when prompted.

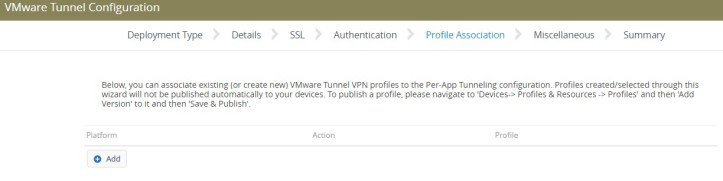
You can create the profile during the configuration, but I would rather create and assign it all together at once separately.
If you have a syslog server, you can configure it here. The default port is 514.

Review the information and click Save.
Back in the Configuration section, you may review the setting in each of the tabs: General, Network Accessibility, and Advanced. If all is well, proceed with the steps below.

Under the General tab, click on Download Virtual Appliance.
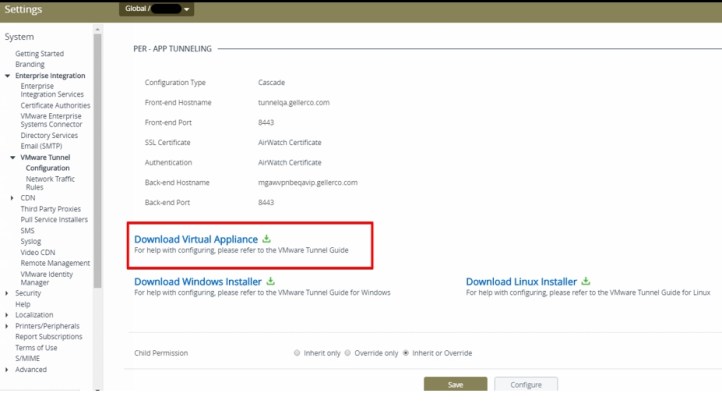
Upon clicking on Download Virtual Appliance, it opens a new tab and directs to this site: https://resources.air-watch.com/view/sbfsfykltpqfxhvg9tpy
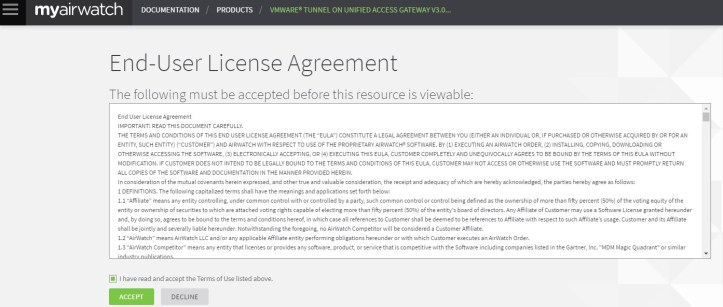
After checking off the box and clicking ACCEPT, you will be taken to another page and download should begin shortly after.

Extract the content of the zip file for import.
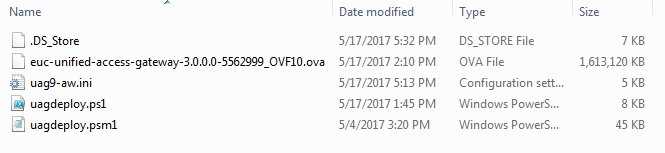
We will now install the VMware Tunnel virtual appliance. The steps are more or less the same for both Relay and Endpoint appliances with the exception of hostname and IP address just to name a few.
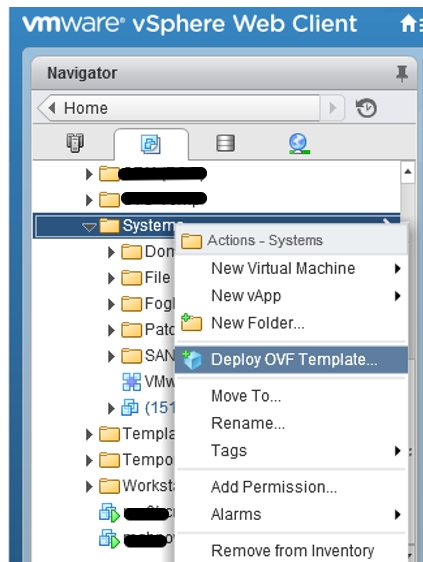
Since this appliance does not support the VMware vSphere desktop client, we will log onto the vSphere web client instead.

From here on, import the virtual appliance as OVF template.
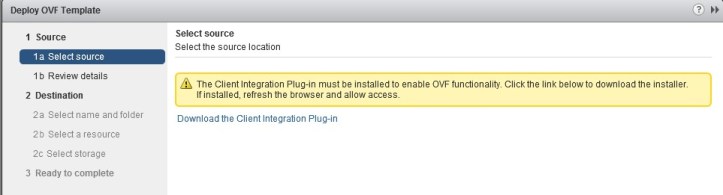
Click Allow when prompted.

If you don’t, you will get the error below.
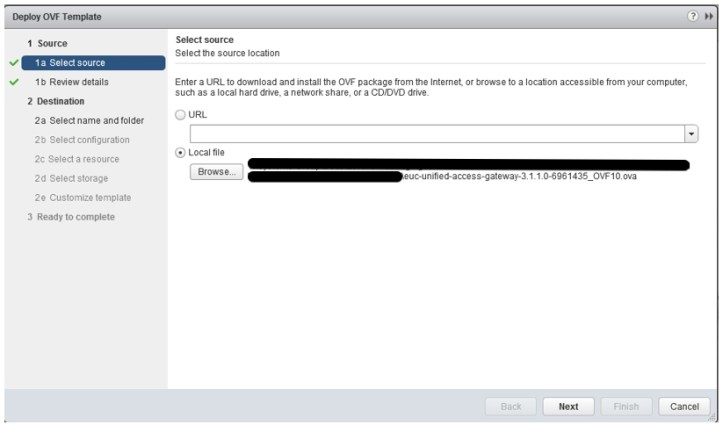
Click Browse and locate the OVA file where you extracted previously from the zip file. Then click Next.
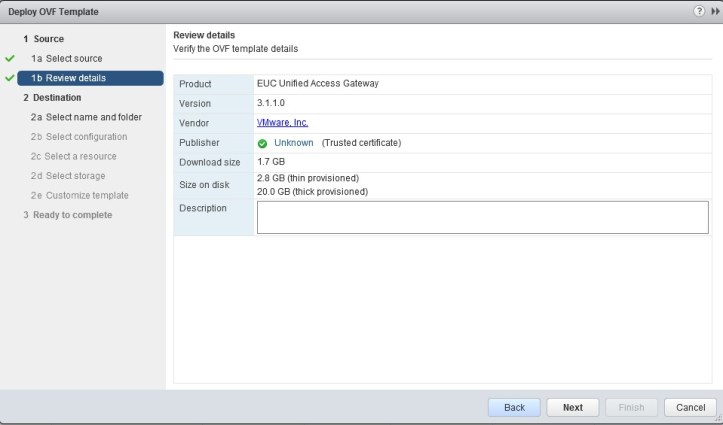
Click Next.
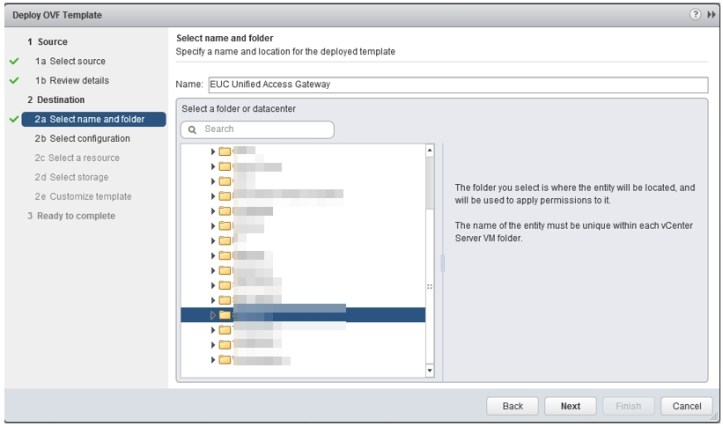
Rename your virtual appliance and select the folder where it will be located. Then click Next.
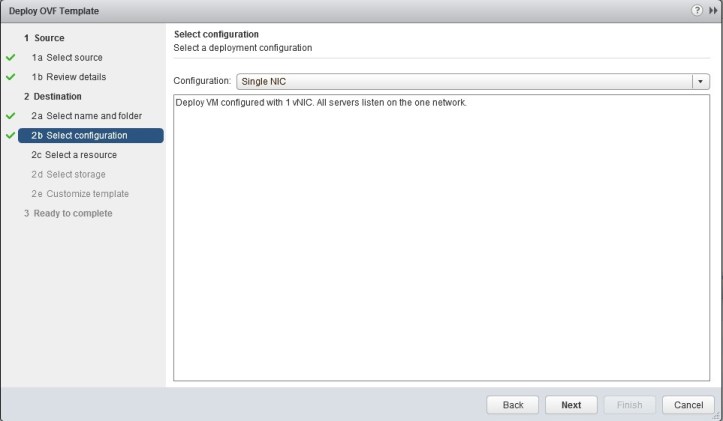
Depending on your networking requirement, select between 1 to 3 NIC configuration. Then click Next.
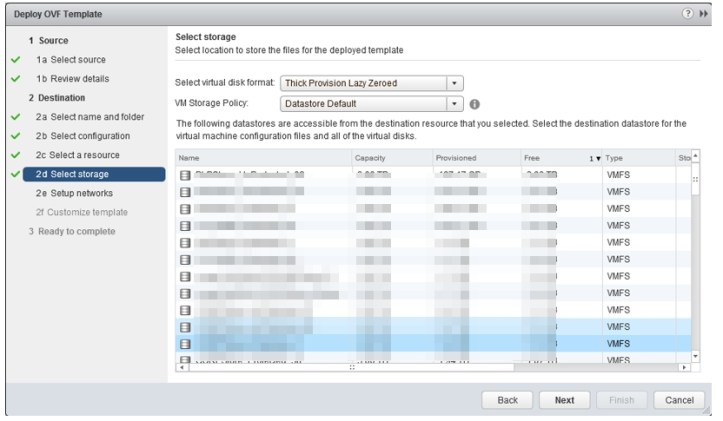
Select the proper option and click Next.

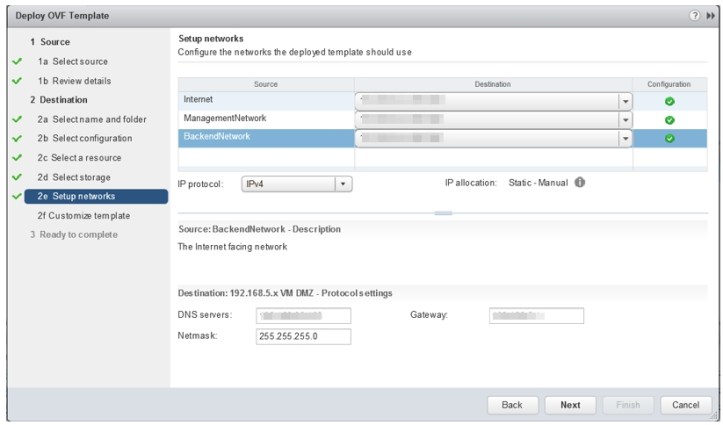
Select the proper option for the networks, and fill in the DNS servers, Netmask, and Gateway. Then click Next.
In the next step, we will configure Networking Properties, CEIP, and Password Options.

For STATIC4/STATICV6 under Networking Properties, it is perfectly fine to leave it blank and it will default to IPv4. Fill in the IP, DNS and Default Gateway again.
If you ever replace the DNS server after the virtual appliance is imported, check out the steps required toward the end of this blog post.


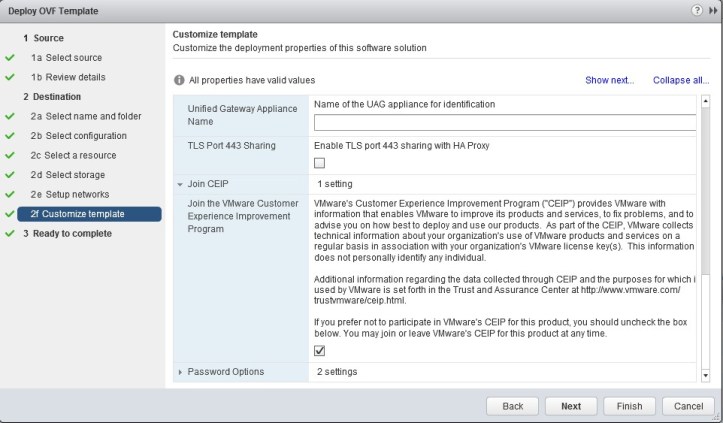
Configure the root user account password and password to log onto the virtual appliance later to finish configuration.

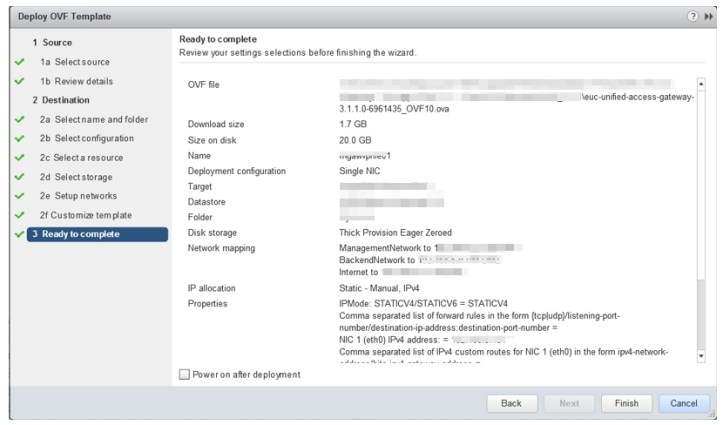
Review all the information once more and click Finish.

Once the virtual appliances have been imported, we can now continue with the configuration. You need to configure each appliance separately.
Open a web browser and go to https://virtual-appliance-hostname:9443/admin.
- Admin Username: admin
- Admin Password: the password you configured earlier under Password Options

Select Configure Manually.
 Click on the below in order.
Click on the below in order.

Click to enable VMware Tunnel Settings.

Fill in the information accordingly and click Save. In the Relay-Endpoint deployment model, the API Server URL and Tunnel Server Hostname should be different between the two virtual appliances.


After clicking Save, you will see the below.
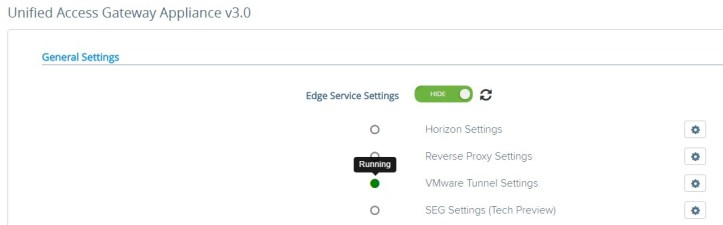
If for some reason the green bubble above does not appear, make sure your virtual appliance is able to communicate with your device service server over port 443. Port 2001 should also be accessible.
- 443 is for the API. The tunnel checks the console for compliant devices, etc.
- 2001 is for the AWCM. AWCM does health checks on the gateway.
- These ports are used to get the white-list of the devices for per -app VPN by doing an API call. When a device makes a request to the VMware Tunnel, the relay server determines if the device is authorized to access the service by doing the API call.
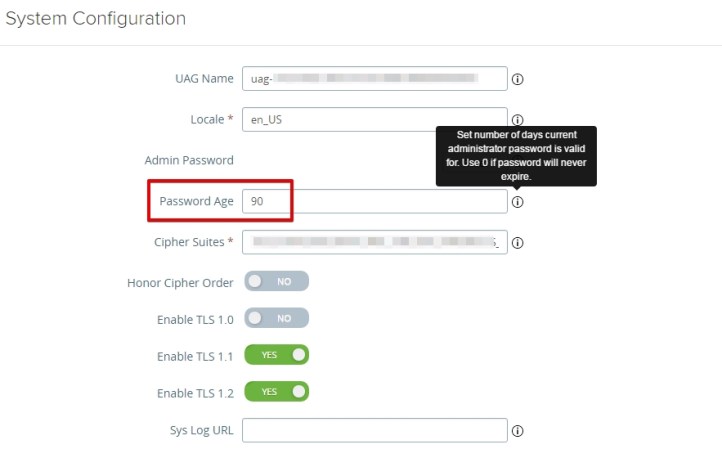
Unless your information security team requires it, I suggest setting the admin password age from the default value of 90 days to never expire.
To do that, from the same page scroll down to Advanced Settings section. Then click on the gearbox icon next to System Configuration.

Next to Password Age, change the default value from 90 (default) to 0 (never expires). Finally, scroll to the bottom of the page and click Save.
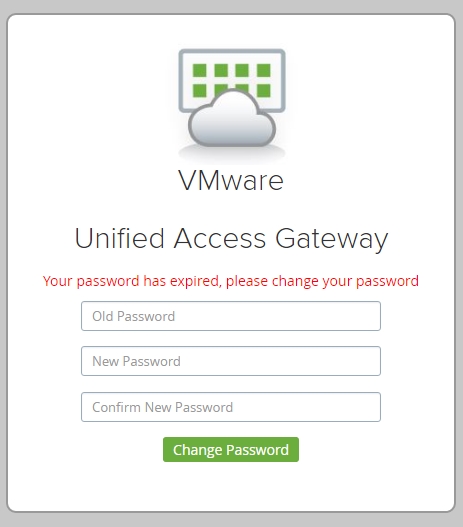
If you do not or forget to change the password age value, you will get the below after 90 days when logging into the console again. Simply change it and you will be able to login with the new password.

If you have multiple appliances to configure, you may export the settings now and then import them back to the new ones. Simply scroll down to the bottom and select Export Unified Access Gateway Settings.

Be sure to rename the files to distinguish between relay and endpoint appliances.

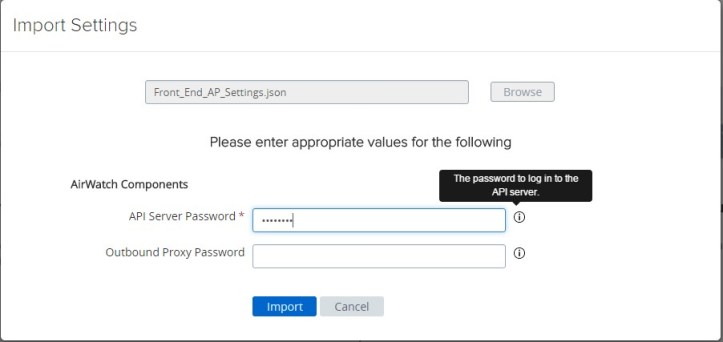
Next time when configuring an upgraded or an additional appliance, choose Import Settings instead of Configure Manually.

Browse for the downloaded export JSON file and click on Import.
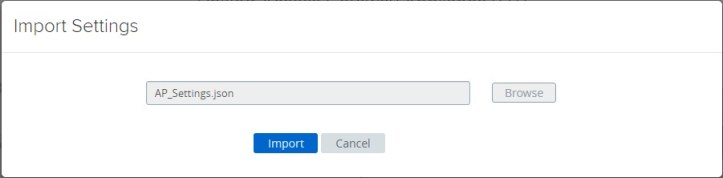
Enter the password and select Import again.
Per AirWatch, the VMware Tunnel app must be present on devices before assigning the VPN profile. In my environment, I deploy iOS apps with Apple Volume Purchase Program (VPP) mainly for silent install, elimination of Apple ID requirement and license tracking.

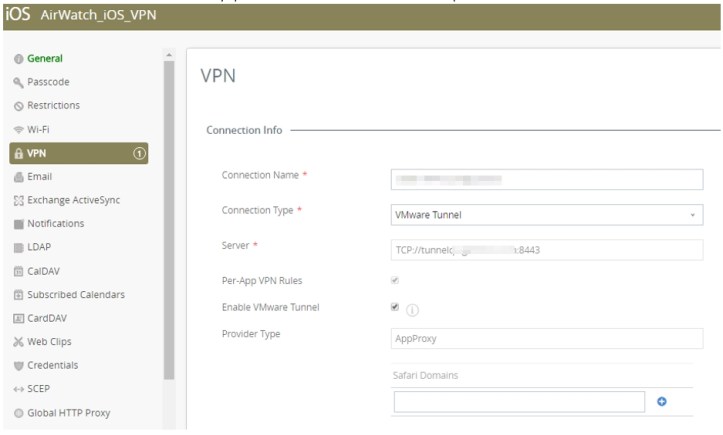
Next up, we will create and deploy the VPN profile. Follow the normal procedure and scroll down to VPN section. Then click Configure under VPN.
Fill in the information accordingly:
- Connection Name: This name will appear within the VPN configuration on the device.
- Connection Type: Select VMware Tunnel
- Server: The external URL accessible by the device
- Enable VMware Tunnel: Check this off to always push the VMware Tunnel version of the profile to the device
Once this profile is deployed, below is what you will see on the iOS device.


For any app to utilize the VMware Tunnel, the proper options must be checked off / selected within the app.
For 3rd party app:
- Check off Use VPN.
- Next to Per-App VPN Profile, click on the drop-down arrow and select the VPN profile you created earlier.

For internal app:
- Within app assignment, select Enabled next to App Tunneling
- Next to Per-App VPN Profile, click on the drop-down arrow and select the VPN profile you created earlier.

Unlike the AirWatch Tunnel app (legacy), it is not necessary to open the VMware Tunnel app at least once on user’s device as it does not require the user to accept user permission.
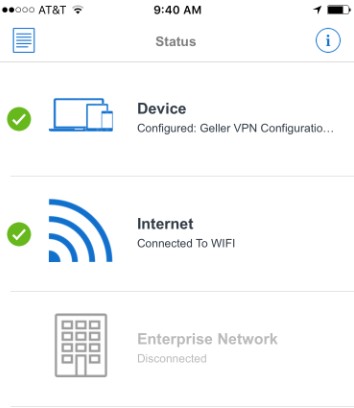
Let’s take a look at what’s inside after launching the VMware Tunnel app.


You may notice that Enterprise Network is shown as Disconnected. It will only be shown as Connected when an app configured to use VPN is running. This connection means the VPN is actively being used.

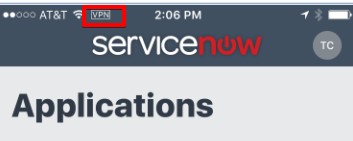
To confirm per-app VPN is working as expected, launch an app that is configured to utilize the VMware Tunnel. Assuming the app does not take up the entire screen upon launch, you should then see the word VPN on the top left corner when communication is established.
If for some reason your app fails to establish the per-app VPN connection, you may try the troubleshooting steps below:
- Review firewall rules and logs
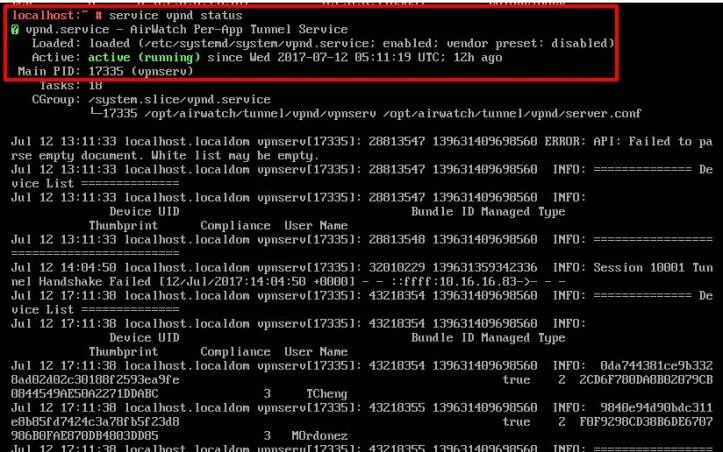
- Log onto virtual appliance with the root account. Then:
- Verify server is listening at port 8443
- Verify and restart service


In addition, a fellow end user computing evangelist, Andrew Morgan, shared the below via his blog post which also helps with monitoring and validating Per-App functionality.
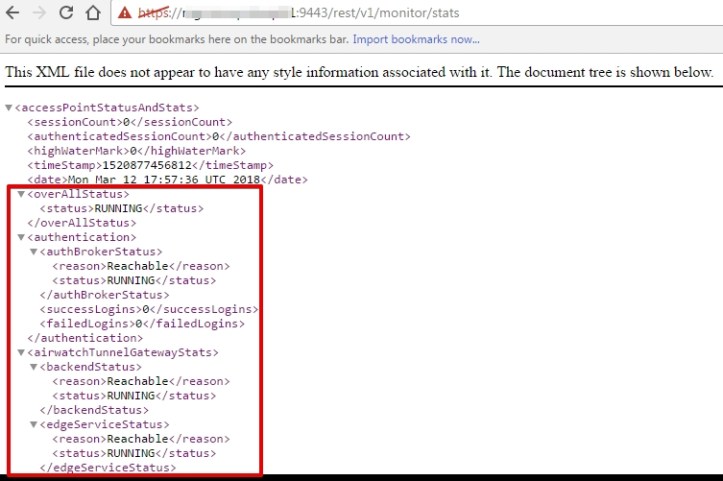
Viewing VMware Unified Access Gateway statistics with REST
In summary, you can view the XML associate with the appliance by visiting https://your-appliance-hostname:9443/rest/v1/monitor/stats.
Here are the steps to take on VMware Tunnel server when DNS server is replaced with a new server.
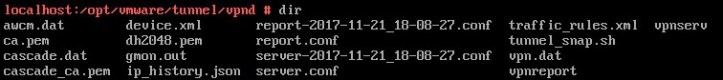
- Navigate to cd/opt/vmware/tunnel/vpnd
- Then vi server.conf
- Modify as needed and hit Escape key
- Type in :wq (this write the file to disk and quit vi)
- Restart the service by doing service vpnd restart

In addition, you may have to do the below.
- Navigate to cd /etc
- Then vi resolv.conf
- Modify as needed and hit Escape key
- Type in :wq (this write the file to disk and quit vi)
- Restart the service by doing service vpnd restart


As always, stay mobile!

Excellent post. Thomas, what is your opinion about TLS Port Sharing? Do you prefer it over using one single host names and separate ports for Per-app and Content?
LikeLike