“Sorry, but I left my Blackberry in the cab/bar/train/hotel.”
Those are the familiar words I often hear from end users, and the first question I would often ask is “Did you try calling the number associated with your device?” It used to work quite well until text message becomes the norm. In VMware AirWatch, we can configure a custom message and contact number on the locked screen of a supervised device with Apple DEP. Hopefully, the finder can then contact and return the device to us.
*As of the writing of this post, Blackberry does not offer the same custom message and contact number option even on the supervised device. A feature enhancement request FER-7057 was submitted in regard.
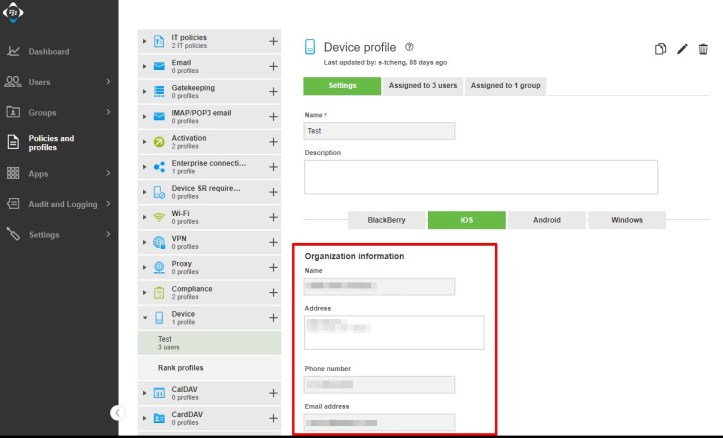
In Blackberry UEM, however, the option to set up a custom message on the locked screen even if the device is supervised with Apple DEP is NOT available. As an alternative, we can specify organization info within a device profile. The screenshot below shows the configuration for iOS. However, it’s pretty much the same for any platform.
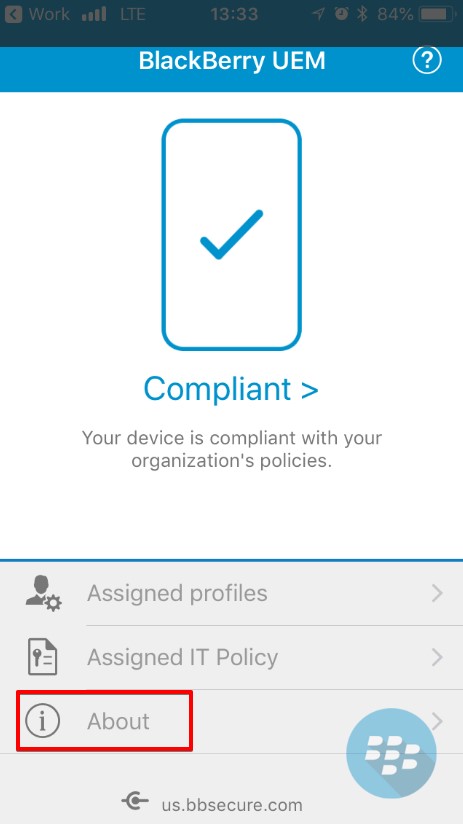
To see this info, you first need to press on the Blackberry Launcher icon. Then select the UEM Client and press About. But what’s the chance that someone will actually go this far to identify and return the device to its rightful owner?
Does that mean we are out of luck? Not exactly as there are few other options both administrators and users can take to avoid possible data leak.
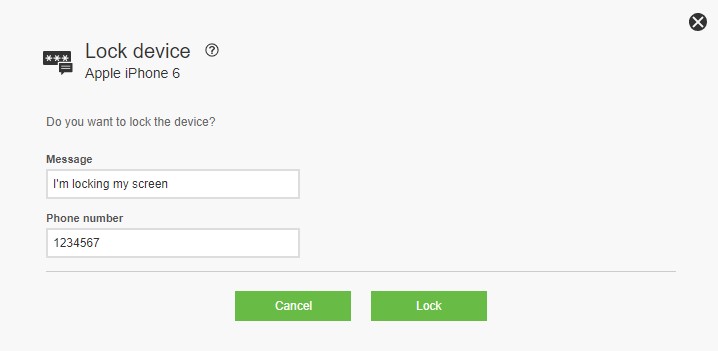
In the UEM console for administrators, the simplest and safest option is to lock the entire device. Once the device is locked, it can be unlocked with the device passcode.
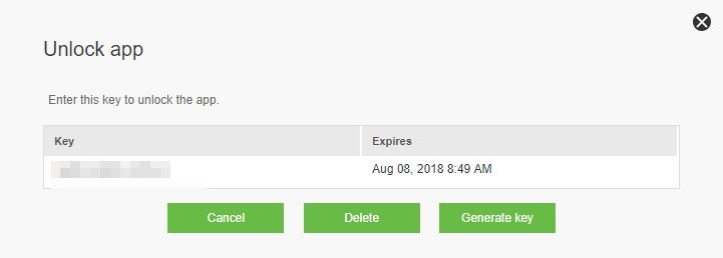
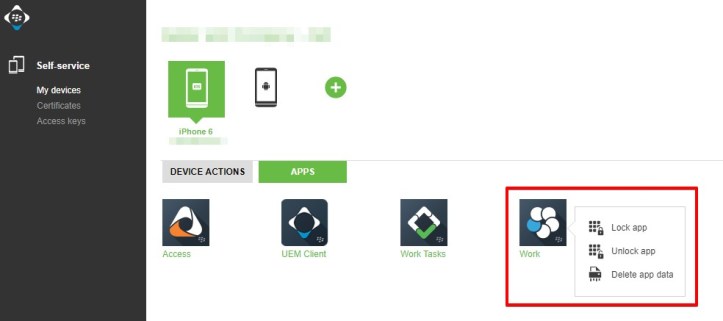
Another option is to lock the Blackberry Dynamics app(s) only. In the case when the device is lost or stolen, I would assume this scenario comes into play if the user simply wants to make sure no one can access his/her work data while leaving the rest of the device untouched.
Once the app is locked, the user will need an unlock key from administrator through the same menu above.
If there’s no hope in getting back the lost/stolen device, I would issue either a data wipe or a device wipe command to ensure that no work data of any kind would fall into the wrong hand. Use this option as a last resort especially with device wipe since it would reset the device back to factory default.
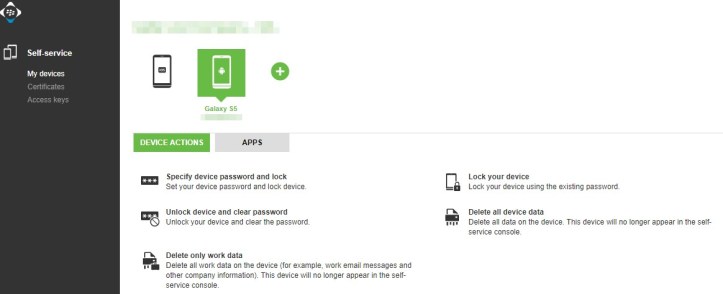
Users can access pretty much the same features through the self-service portal. Here’s a list of commands a user can send to his/her device.
While the kind of action a user can take is the same for both cloud-based and on-premises customer, however, the URL to access your self-service will vary. Below are a couple of examples.
- Cloud-based – https://portal1.emm.blackberry.com/mydevice?tenant=SRPID

- On-premises – https://your-UEM-host:443/mydevice

Notice how the list of actions can vary depending on the device’s platform.
Here’s list of actions the user can take with the app.
As always, stay mobile!